RADIX-ST
Static Security Analysis
Identify and resolve security weaknesses earlier in chip design.
Uncover Hardware Security Risks With Greater Efficiency
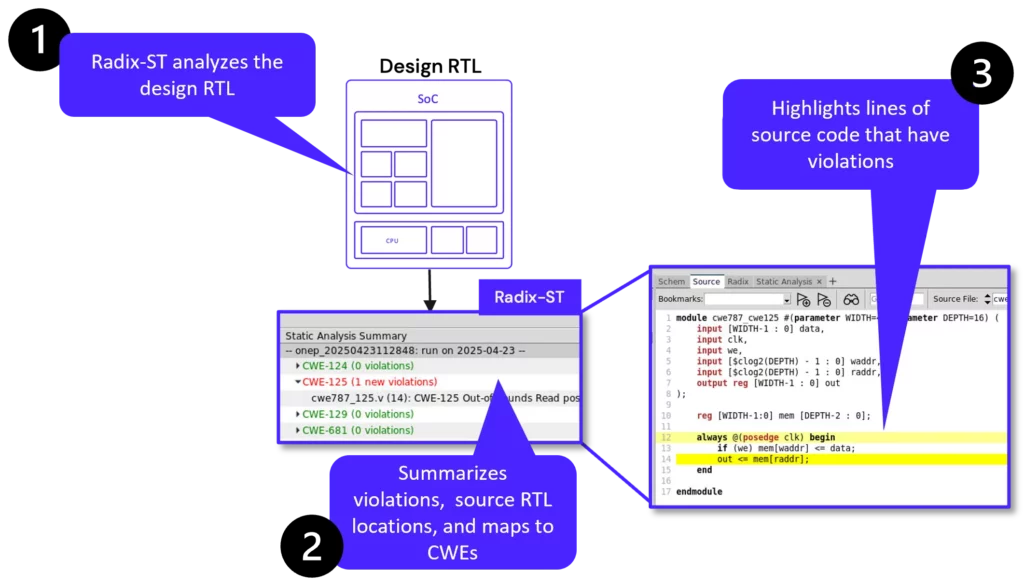
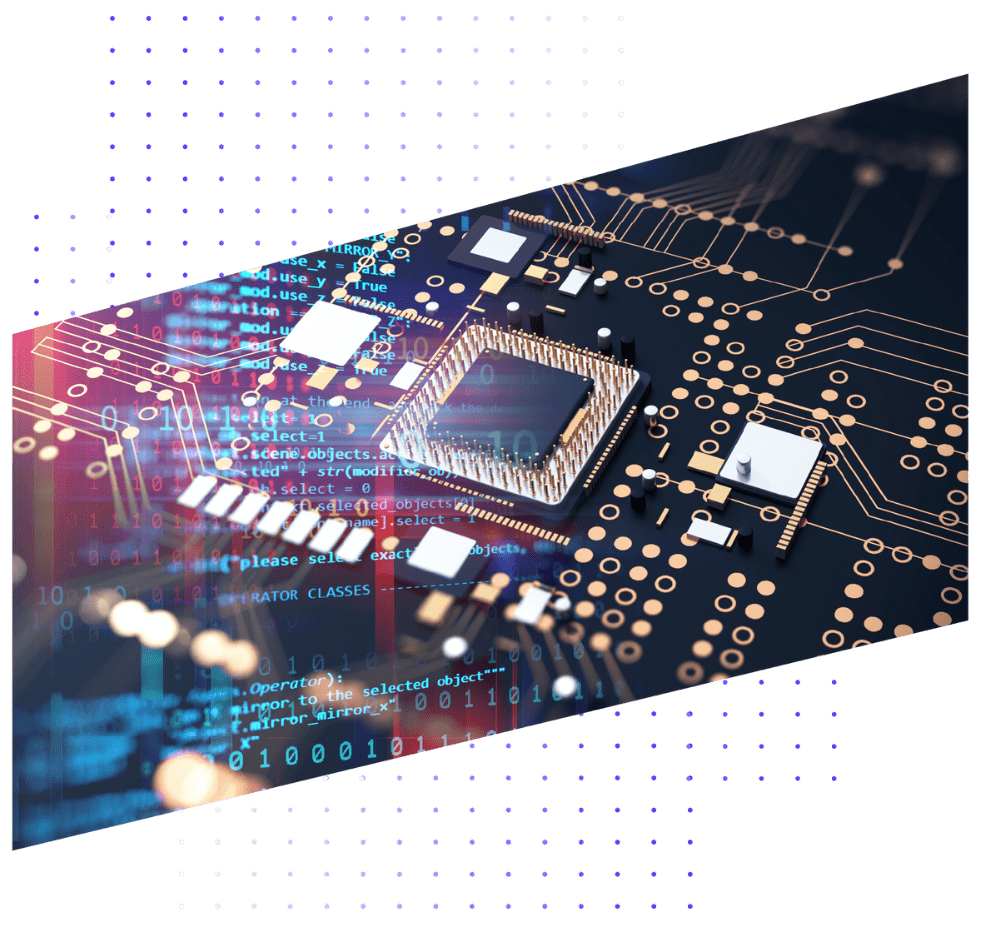
Radix-ST is a static security analyzer designed to identify potential design weaknesses early in the development lifecycle without requiring simulation or emulation.
Unlike basic source code linting tools, Radix-ST performs deep security analysis of your RTL designs, seamlessly integrating with the Radix security assurance workflow to deliver actionable vulnerability insights that pinpoint the location of security issues in the source code and map them to relevant hardware Common Weakness Enumeration (CWEs).
Radix-ST Benefits:
Early Security Analysis
Identify and rectify security vulnerabilities at the earliest stages of development, with minimal user input.
Focused Security Insights
Utilize the Common Weakness Enumeration (CWE) knowledgebase to acquire in-depth knowledge of potential security vulnerabilities and ensure that designs adhere to industry best practices.
Seamless Integration with Radix Workflow
Leverage the Radix-ST aligned workflow and GUI with Radix-S and Radix-M to comprehensively execute security verification from the initial RTL code to system integration.
Radix-ST Features:
Automated RTL Inspection
No test bench or constraints required.
Proprietary Detection Engines
High accuracy, minimal false positives.
Integrated Reporting
Highlighted violations within the RADIX GUI.

Cross-view Navigation
Interact across Radix source, schematic, and cone views.
Radix-ST Workflow
Use Cases
As the complexity of chip design grows, so do threats that can undermine customer trust—and your bottom line. See how Cycuity can give your business end-to-end hardware security throughout the product life cycle.
Roots of Trust
Hardware roots of trust have become the foundation of semiconductor security. See how you can build a more secure system with hardware security assurance from Cycuity.
Application Processors
Modern microprocessors are core to the applications that power cars, data centers, and mobile phones. As their performance has grown, so have their vulnerabilities.
System-On-Chips
Fundamental to the security of IoT, automotive, and datacenters is the security of the SoCs that power them. Verify the security of increasingly complex SoCs with Radix
Microcontrollers
Microcontrollers are responsible for the core functionality of embedded devices in consumer electronics, cars, medical devices and more. Securing their operation is critical for product safety and security.
Cybersecurity Compliance
As regulations evolve to keep pace with innovation, ensure that your hardware not only complies with existing frameworks but is also resilient against future hardware security challenges.
Incorporating CWE
The industry’s formal list of common hardware weaknesses is the Common Weakness Enumeration (CWE), a list created and curated by MITRE. For organizations seeking a “secure by design” approach, testing against the CWE list is critical.
See How Radix-ST Can Improve Your Security
Hardware security is a journey. Where are you in the maturity of your hardware security?
